Remember the days when identifying an email scam was as simple as spotting a misspelled word or a bizarre request from a fictional foreign prince? Those days are officially over. Today, cybercriminals don’t need poor grammar to trick you; they have artificial intelligence, deepfakes, and a terrifying level of precision.
In 2026, Phishing Attacks have evolved from a numbers game into highly targeted, personalized, and automated psychological warfare. According to recent Global Cybersecurity Outlook reports, the rapid integration of AI into cybercrime has made these attacks the fastest-growing digital risk worldwide.
Whether you are a busy executive, a healthcare provider, or an everyday internet user, the barrier between a secure network and a catastrophic data breach is often a single, flawlessly crafted message. In this post, we will dive deep into how these attacks have transformed, what the data tells us about the current landscape, and how you can stay one step ahead of the modern scammer.
Then vs. Now: The Evolution of the Phishing Threat
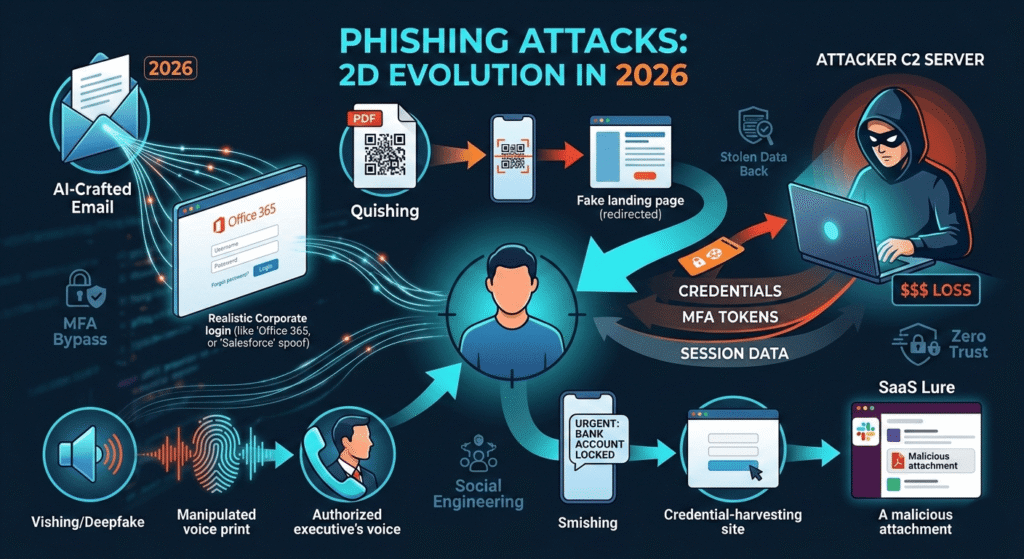
To understand the severity of the current landscape, we must look at how drastically the tactics have changed over the last few years. The spray-and-pray method has been entirely replaced by hyper-personalized, omni-channel assaults.
Comparison: Traditional vs. Modern Phishing
| Feature | Traditional Phishing (Pre-2022) | Modern Phishing (2025–2026) |
| Primary Medium | Email (Spam filters caught most) | Omni-channel (SMS, LinkedIn, Slack, QR Codes) |
| Creation Time | Hours to days of manual drafting | Under 5 minutes using generative AI |
| Tell-Tale Signs | Poor grammar, generic greetings | Flawless grammar, highly contextualized |
| Authentication Evasion | Defeated by basic Multi-Factor Auth (MFA) | Uses AiTM (Adversary-in-the-Middle) to bypass MFA |
| Impersonation | Fake corporate logos and spoofed emails | Real-time AI voice/video deepfakes of executives |
As the table illustrates, the modernization of these threats is alarming. Attackers are no longer just guessing your bank; they are scraping your LinkedIn, analyzing your recent projects, and crafting a lure that fits seamlessly into your daily workflow.
Key Insights: The Anatomy of Modern Phishing Attacks
The sheer volume of attacks is staggering. Threat intelligence shows that over 90% of all data breaches still begin with a social engineering lure. But it’s not just the frequency that has changed—it is the methodology. Here are the key insights defining the current threat landscape.
1. The Terrifying Speed of AI
Generative AI has democratized cybercrime. Historically, a sophisticated spear-phishing campaign required significant time—researching a target, building a fake landing page, and crafting a believable narrative. IBM X-Force researchers demonstrated that AI can generate highly convincing campaigns in just five minutes, compared to the 16 hours it typically took human operators.
This 192x improvement in efficiency means threat actors can spin up thousands of unique, polymorphic emails that easily evade traditional signature-based spam filters. By the time a malicious domain is flagged and blocked, the AI has already generated a dozen more.
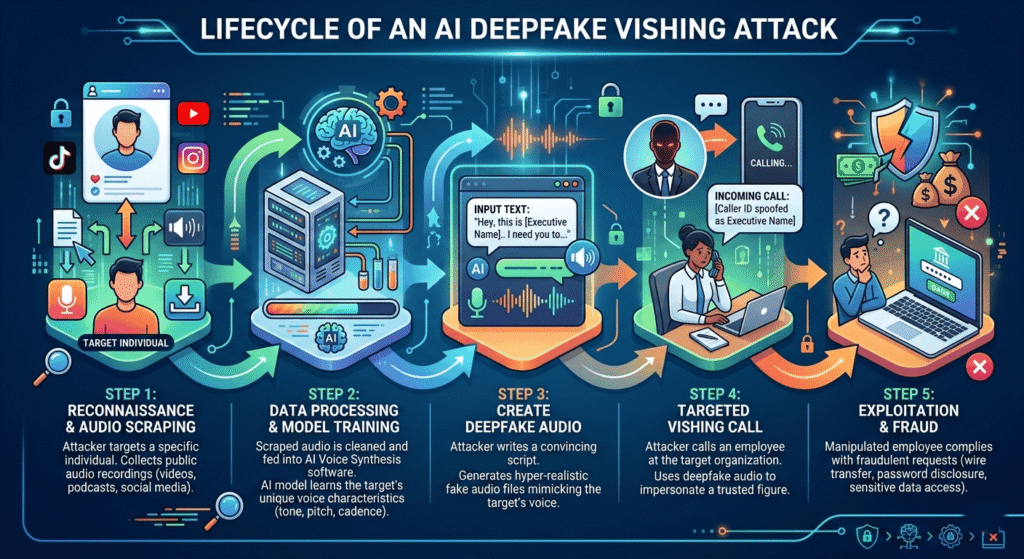
2. Deepfakes and Vishing: When Seeing Isn’t Believing
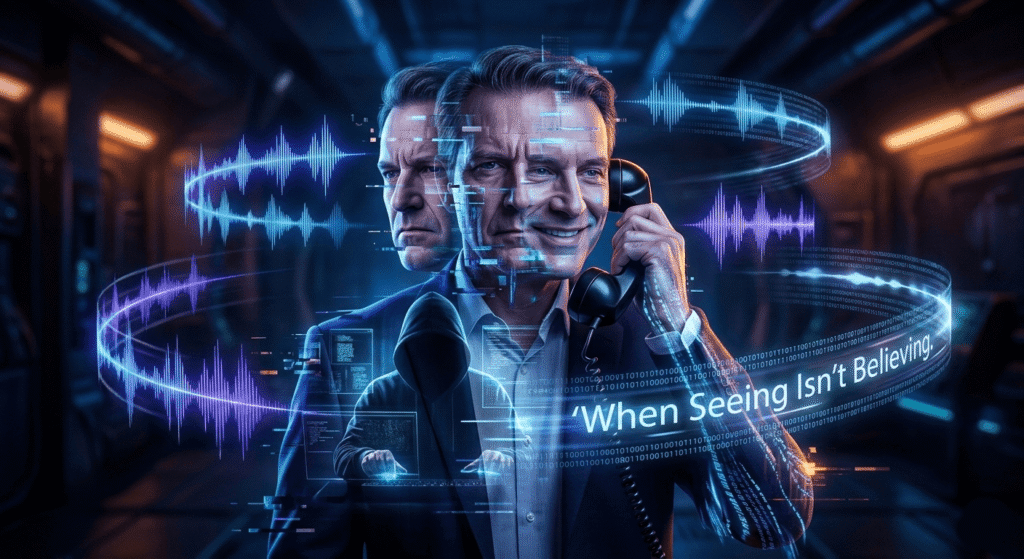
You receive a frantic voice note from your CEO on WhatsApp. They are stuck in an airport and need you to urgently wire funds to a vendor to secure a critical contract. The voice sounds exactly like them—the pacing, the tone, the subtle accent.
3. The $4.88 Million Price Tag
This is “vishing” (voice phishing) powered by AI voice cloning. Attackers only need a few seconds of public audio—often scraped from a corporate podcast or a YouTube presentation—to create a hyper-realistic voice clone. We are also seeing a rise in deepfake video calls used to authorize massive financial transfers, fundamentally breaking the trust we place in our own eyes and ears.
The financial consequences of falling for a scam have never been higher. According to recent data, the average cost of a phishing-related data breach has climbed to a staggering $4.88 million. For U.S.-based organizations, that number routinely eclipses $10 million.
These costs extend far beyond the immediate theft of funds. They include regulatory fines, operational downtime, incident response fees, and devastating long-term reputational damage. When an attack escalates into ransomware—which happens in over half of all successful phishing breaches—the organizational paralysis can last for weeks.
4. Omni-Channel Threats: Beyond the Inbox
If you are only looking for threats in your email inbox, you are leaving your back door wide open. Phishing attacks have gone omni-channel, exploiting platforms where our guard is naturally lower.
- Quishing (QR Code Phishing): Attackers place malicious QR codes on legitimate signage, parking meters, or embedded in seemingly harmless PDF documents. Scanning them bypasses email security entirely, redirecting victims to credential-harvesting sites on their mobile devices.
- Smishing (SMS Phishing): Urgent text messages about “failed package deliveries” or “locked bank accounts” continue to surge, exploiting the immediacy of text messaging.
- SaaS Collaboration Lures: Hackers are increasingly targeting users directly inside trusted applications like Microsoft Teams, Slack, and LinkedIn, leveraging compromised internal accounts to spread malware to colleagues.
5. MFA is No Longer a Silver Bullet
For years, security professionals preached that Multi-Factor Authentication (MFA) was the ultimate defense. Unfortunately, cybercriminals have adapted.
Phishing-as-a-Service (PhaaS) platforms have automated Adversary-in-the-Middle (AiTM) attacks. When a user clicks a malicious link, they are taken to a proxy site that perfectly mimics their corporate login. The user enters their password and their MFA code. The attacker’s proxy instantly passes these to the legitimate site, logs in, and steals the active session token.
While international task forces have had recent successes—such as the early 2026 disruption of the massive Tycoon 2FA platform—the underlying tactic of token theft remains a dominant threat.
How to Fortify Your Defenses in 2026
The reality is that human error can never be patched out entirely. However, you can significantly shrink your attack surface by adopting a modern, defense-in-depth strategy.
Shift to Phishing-Resistant MFA
Traditional SMS codes and push notifications are easily intercepted or bypassed via “MFA fatigue” attacks. Organizations must transition to phishing-resistant authentication methods, such as FIDO2 security keys or passkeys, which rely on cryptographic hardware rather than easily stolen codes.
Implement AI-Driven Email Security
To fight AI, you must use AI. Legacy email gateways rely on outdated blocklists. Modern security tools use behavioral AI to analyze communication patterns, tone, and metadata to flag anomalies. If an email from your “CFO” suddenly originates from an unusual IP address and uses atypical phrasing, the system quarantines it before it reaches the inbox.
Adopt a Zero-Trust Architecture
Assume breach. A Zero-Trust model ensures that even if an attacker successfully phishes an employee’s credentials, their lateral movement within your network is severely restricted. Implement strict principle-of-least-privilege access and require continuous verification for all users.
Evolve Your Security Awareness Training
Annual, compliance-box-ticking cybersecurity training is dead. Employees need short, continuous, and context-aware micro-learning. Training must simulate modern threats—including deepfakes, SMS lures, and QR code manipulation—so staff can develop a healthy, “politely paranoid” baseline of skepticism.
Conclusion
Phishing attacks have fundamentally transformed from clumsy, mass-market scams into highly engineered, AI-driven precision strikes. The speed of attack deployment, the rise of deepfake impersonations, and the circumvention of traditional MFA protocols paint a sobering picture of the 2026 threat landscape.
However, by understanding the mechanics of these modern attacks, acknowledging that threats extend far beyond the email inbox, and investing in resilient, AI-powered defenses, organizations can protect their data and their people. In this new era of deception, education and proactive technology are your strongest shields.